Risk Management Enterprise for Beginners
An Unbiased View of Risk Management Enterprise
Table of ContentsSome Known Questions About Risk Management Enterprise.9 Simple Techniques For Risk Management EnterpriseRumored Buzz on Risk Management Enterprise
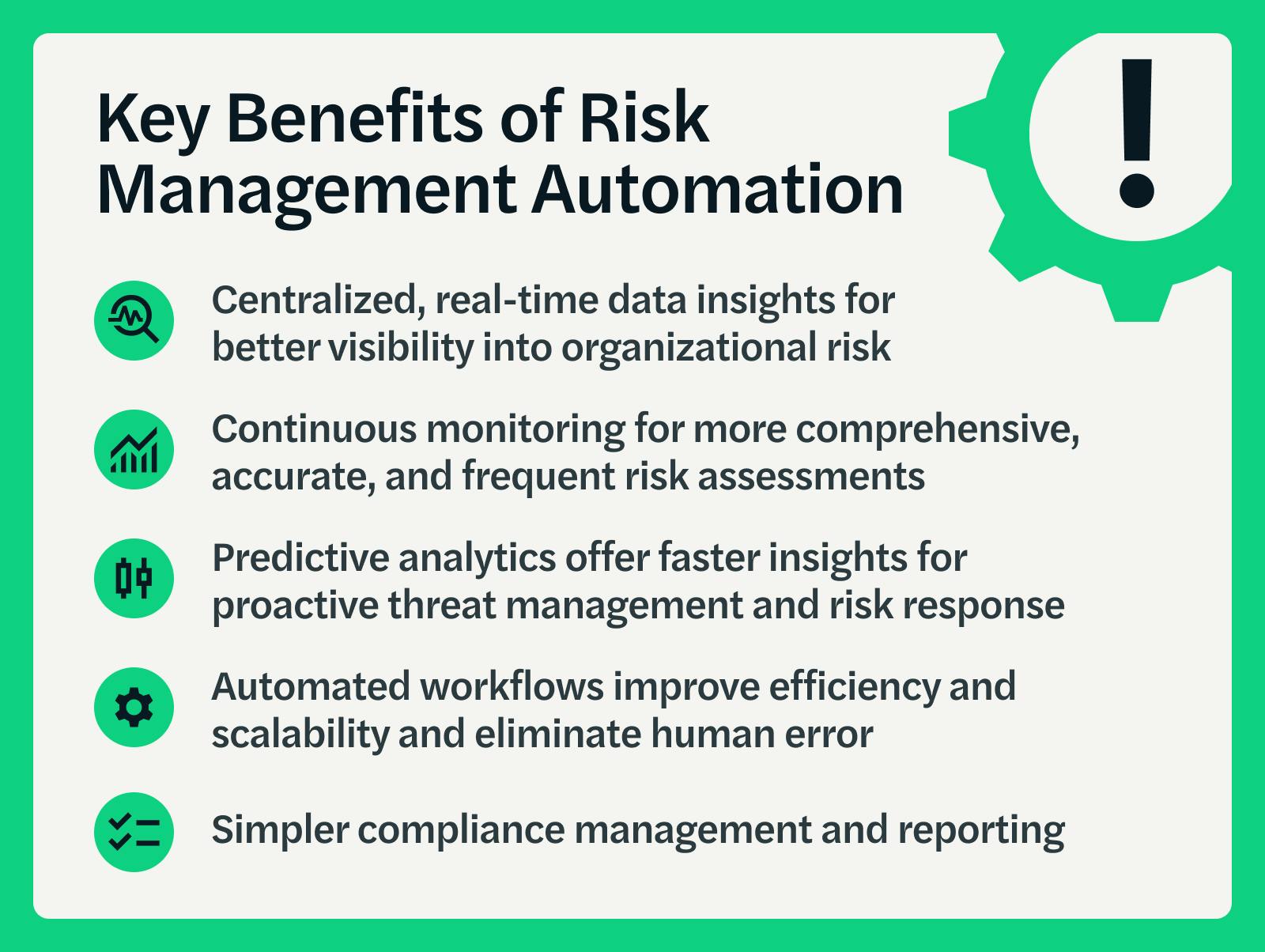
Control that can see or modify these elements by establishing specific accessibility rights for private customers, guaranteeing information safety and security and customized use. Allows users to customize their interface by selecting and organizing essential data components. Gives a customized experience by permitting modification of where and just how data elements are presented.It enables accessibility to real-time incorporated data instantly. Risk Management Enterprise. This aids get rid of squandered time on manual report collection. Likewise, centers can utilize extensive information knowledge for quicker and extra educated decision-making. It enables the automatic production of stakeholder records for individuals or groups. Allows timely decision-making and decreases delays triggered by out-of-date details.
Diligent is a threat administration software program that permits enhancing efficiency, and enhances development. It also helps keep an eye on dangers with ERM software application that includes incorporated analytics and adapts to your company needs.
Not known Details About Risk Management Enterprise
It additionally supplies one-click records. Moreover, it gives your management and board the real-time understandings they need. Simplifies the process of collecting threat information from different parts of the company. Risk Management Enterprise. It permits for easy modification of reports and storyboards. Gives leadership and the board with real-time threat insights. Usage ACL's innovative analytics to spot risk patterns and anticipate hazards.
This allows business to catch danger insights and red flags in the third-party vendor's security record. This permits conserving danger assessments as auditable records. It also permits exporting them as PDFs. To complete the process companies can complete a reassessment day. Makes it possible for firms to catch and record threat insights and red flags in third-party supplier protection reports.
It likewise lowers threat with structured conformity and threat monitoring. It can aid collect and track all your risks in the Hyperproof danger register.
It provides fast access to necessary details and paperwork. This makes sure the security of Active proof circumstances by allowing multi-factor authentication (MFA) using authenticator apps such as Google Authenticator, see Microsoft Authenticator, or Authy.
3 Easy Facts About Risk Management Enterprise Described
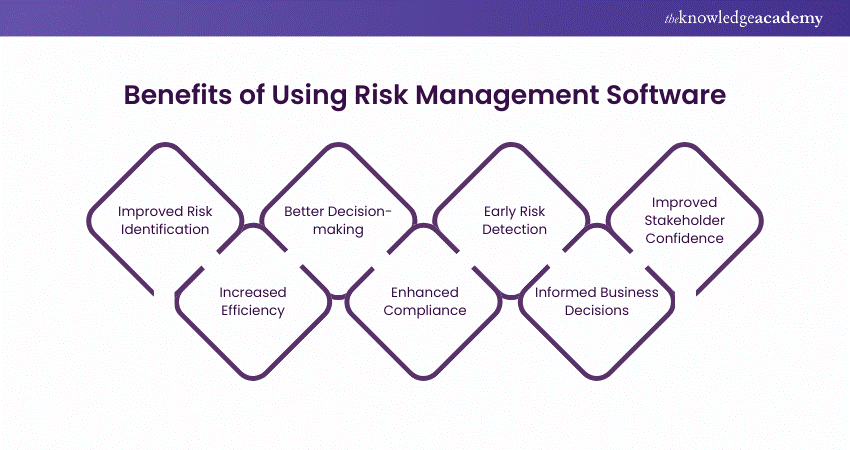
It supplies top-tier safety attributes to safeguard sensitive information. This threat monitoring software is a perfect tool for facilities looking to take care of unnecessary issues or risks.
Users can likewise use the AI-powered devices and pre-existing material to produce, review, prioritize, and address dangers successfully. click for more Simplifies the process of setting up and populating threat registers.